Co-Design Spaces for Explanation Interfaces
Explainable artificial intelligence (XAI) shall support humans with making more informed decisions mitigating black box effects of machine learning (ML) models. Transparency is a key requirement for acceptance and adoption of algorithmic decision support, especially in expert domains such as healthcare or jurisdiction where decision making comes with substantial risk. To this end, AI explanations must be understandable and meaningful for users other than AI/ML experts. In other words, explanations of AI/ML system’s advice must be presented to users as interfaces in such a way as to maximize interpretability and minimize bias. To achieve this complex goal, a systematic human-centered approach for designing explanation interfaces is paramount.
The PhD project investigates how participatory design methods can be used to design representations of explanations (interfaces) produced by machine learning processes in such ways as to promote more informed decision-making behavior and mitigate possible bias effects. In particular, the domain of medical decision making is considered.
Contributions to a Reference Architecture for Federal Cybersecurity Management
The information technology of the new millennium is characterised by changing framework conditions for the state, economy and society. In particular, the globalisation of production processes, the more flexible workplace design of employees in terms of location and time, the fundamental technological changes towards cloud computing, increasing digitalisation and the use of AI systems are having a lasting impact on the traditional view of information and communication systems. The dependence on the supply chain is blatant, while at the same time the expectation of uninterrupted availability of ICT systems is often. Companies as well as state institutions must face up to these challenges in order to provide adequate collective protection against threats on the one hand and to protect the economy and society in this order on the other. Information security is therefore important and indispensable for all organisations. The state has a coordinating role to play here.
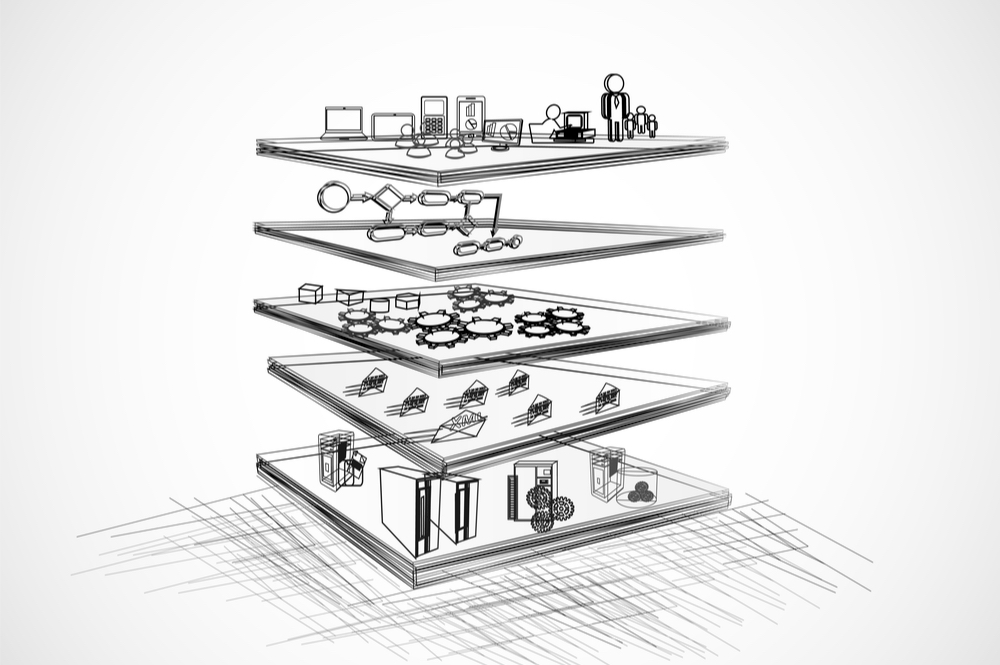
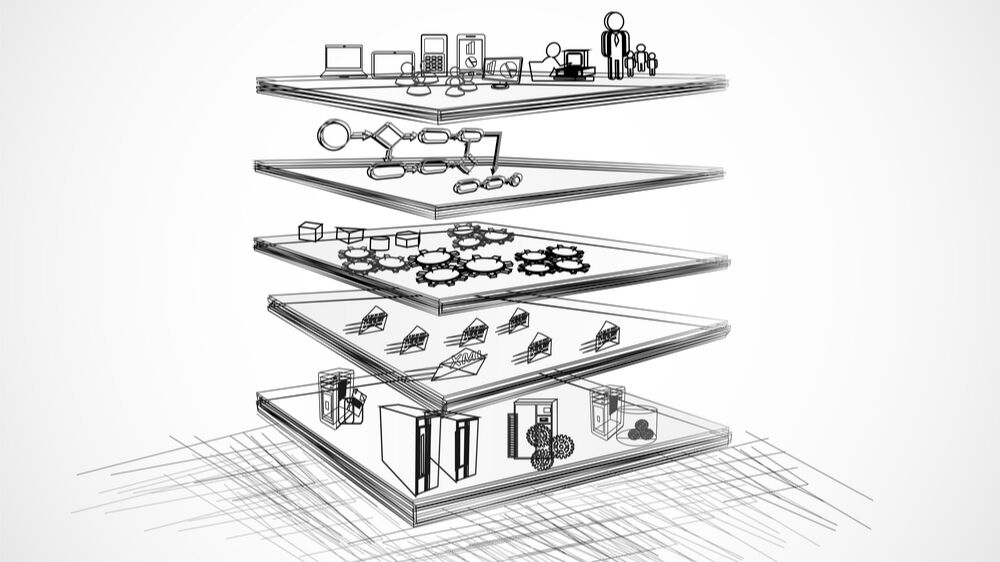
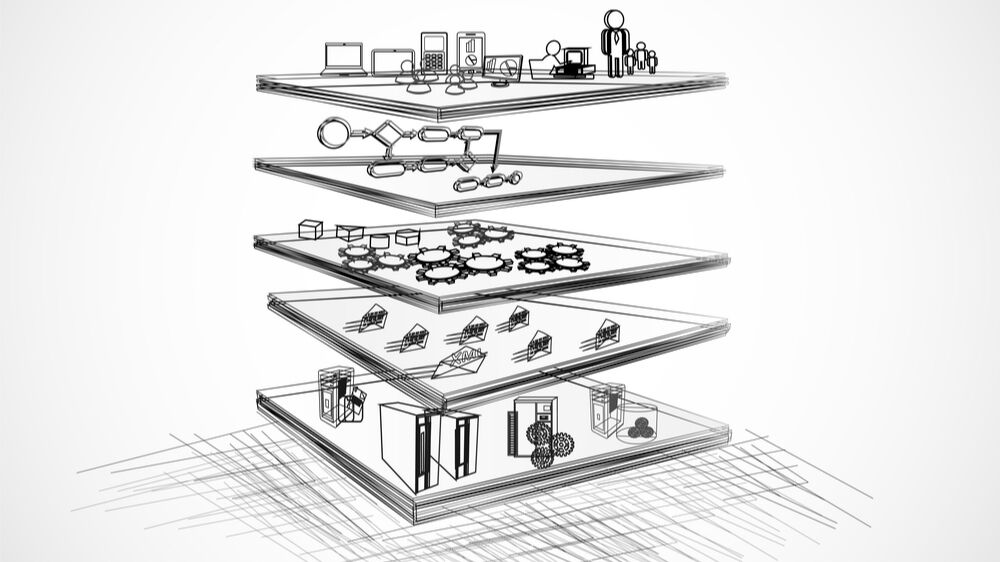
Considering the opportunities and the wide-ranging research in the field of information security, an enterprise architecture – transferred to public administration – should make an accepted and appropriate contribution to continuously strengthening services of general interest. Organisational structures are needed that are adapted from corporate development and researched and adapted to the requirements of the state in order to withstand the change processes of information technology. This research work in the field of enterprise architecture management is carried out along the lines of design science research. In principle, the result of the research work proposes a reference model in the federal context of Germany, which meets the challenges of a dynamically changing IT landscape with an increasing threat situation. This thesis applies the design science research process to propose a reference architecture. It is a problem solution from the practical environment of the ministerial state administrations in Germany. The research process is carried out in iterative steps, from the requirements analysis to the evaluation of the results and their publication.
Procedural model for the adoption of ISMS in small public sector organisations
Threats from cyberspace are increasing more and more. These threats aKect not only companies but also administrations. The automated processing of information and data now plays a crucial role in fulfilling tasks in local governments. The complexity of information technology, the increasing degree of networking, and the dependence on ITsupported processes require that the security of information technology has an ever-higher priority. Due to the increased dependence on modern ICT, the risk of information infrastructures being impaired by deliberate attacks from within and outside, negligent actions, ignorance, or technical failure has increased significantly, both qualitatively and quantitatively. Small local governments face the same risks as large organisations but are more vulnerable at any given time due to reduced resources.
Previous research work focuses on the framework conditions of the corporate environment. These frameworks cannot transfer to administrations without revision, and thus, provided concepts, strategies, or even recommendations for action were not suitable to the requirements of governments.
This thesis develops, describes and evaluates a procedural model with a supporting software component for developing and establishing an information security management system for the target group of small local governments.
In this way, the framework conditions, designs and eKects of implementing the process model can be shown and examined both in science and practice. The procedural model was tested on 24 test subjects under natural conditions and extended to other clients over time.
The overall development of the concept was implemented with the help of data mining tools to react proactively to changes in the environment and threat scenarios from cyberspace and thus ensure the organisation's resilience in the long term.
The thesis uses a design science approach as an overarching research paradigm. In summary, implications, limitations and possibilities for future research are derived.
Quantified Vehicles: Data, Services, Ecosystems
Digitalization has become an important driver of service and business innovation in the automotive industry. For instance, the Quantified-Self movement has recently been transferred to the automotive domain, resulting in the provision of novel digital services for various stakeholders including e.g. individual drivers and insurance companies. In this direction, a growing number of ICT start-ups from outside Europe have entered the market, and thereby raised awareness of the automotive industry, that in the age of digital technology vehicles will have to exceed their former functionality as a tool for transportation to survive as status symbols. One feasible approach is to provide valuable digital services based on vehicle sensor data which currently is used for the sake of driving only – termed “quantified vehicles”.
The aim of this research is amongst others to analyze vehicle sensor data (data types, availability across manufacturers, interfaces), stakeholders, business models and value models, and the vehicle data value chain, and to design and implement a data acquisition hardware and software, a scalable software architecture for data analysis, and data-driven services. Based on that, scenarios for vehicle data ecosystems will be developed.
Homepage/Blog with news regarding progress of the dissertation project: http://www.christiankaiser.at/
Design Principles for Ensuring Compliance in Business Processes
In contrast to process modeling, the modeling of legal requirements requires not only an understanding of processes but also a basic understanding of legal concepts for the interpretation of regulations. However, while process modelers and analysts who are trained in using formal methods may be experts in applying process logic, they do not necessarily understand the normative meanings of a regulation. Modeling languages that help this user group to identify relevant concepts are hence a great advantage in compliance modeling to avoid modeling errors. Paradoxically, these rule languages, also referred to as compliance languages, have yet to be evaluated in terms of their representational or cognitive complexity, so it is impossible to say whether these languages can be efficiently used. In this thesis, we close this research gap and evaluate the complexity and understandability of compliance languages. First, to calculate the complexity, we apply established software metrics and interpret the results with respect to the languages’ expressiveness. As a measure of their expressiveness, we distinguish the normative concepts of legal requirements. Second, to investigate the languages’ understandability, we use a cognitive model of the human problem-solving process and analyze how efficiently users perform a compliance modeling task. Our results have theoretical and practical implications that give directions for the development of compliance languages, and rule-based languages in general.
Conceptualisation and Instruments of preventive returns management in business-to-consumer E-Commerce
The trade of goods via the Internet is continuously increasing. As a result, the number of returns in e-commerce is also rising steadily. Especially in the German business-to-consumer online trade, returns are a great challenge and very cost-intensive. Preventive returns management attempts to prevent returns by starting before the goods are delivered. Thus, it contributes to increasing competitiveness and, if necessary, customer satisfaction. Previous research work was oriented towards conditions abroad that are difficult to transfer and did not provide a comprehensive picture of preventive returns management in the German market. This thesis develops a conceptual framework for preventive returns management in e-commerce. Through this framework, the conditions, design possibilities as well as the effects of preventive returns management can be made visible and evaluated both in science and practice. The work uses a design science approach as a superordinate research paradigm. In addition to qualitative and quantitative studies, approaches from the field of machine learning (e.g. text mining, SVM) were implemented and evaluated. Significant identified design possibilities can be directly implemented in the respective IT processes of the online shop. Above all, rigidly implemented decision-making processes should be changed towards more dynamic IT processes. Furthermore, implementation recommendations for online shops were derived, which can be scientifically proven as well as substantiated by implementations tested in practice.
A Method for the Design of IT Self-Services in organizational settings
Business analysts praise Development and Information Technology (IT) Operations (DevOps) as one of several approaches underpinning digital business. DevOps describes the effort to integrate software development and IT Operations. This integration enables software developers to perform IT Operations tasks on their own, thereby incorporating the IT self-service paradigm.
Through IT self-service (e.g., cloud service provisioning and automated software deployment) internal customers (e.g., software engineers and IT consultants) become actively involved in the process of IT service delivery. In other words, IT self-service enables the IT department to transfer task-performance to internal customers. For the IT department, this can translate into an improved efficiency from a reduced workload of the IT personnel. IT self-service is about freeing the IT personnel from performing recurrent, routine IT service delivery tasks. It allows to reduce the time the IT department must spend on operational tasks, thereby enabling it to spend more time on a strategic contribution for the organization. To realize such benefits, IT self-services must be designed properly from the IT Operations perspective. So far, academic research has fallen short in guiding service providers on how to design self-services to reduce the service personnel’s workload in service delivery. Hence, scholars call for research that provides guidance for managerial decisions on which services tasks to automate and which customers to address with self-services.
This research follows this call. The goal of this research is to develop a method, which guides IT decision makers in designing IT self-services to reduce the IT personnel’s workload in IT service delivery, based on decision theory principles. The design of the method follows the Design Science Research paradigm. To evaluate the method, it is planned to be instantiated in the form of a decision support system.
Decision Support in Enterprise Architecture Management
In times of very dynamic markets, enterprises are faced with major challenges. New business models and newly emerging competitors are tantalizing the competition and shifting market shares. Product life cycles are becoming shorter and shorter. Enterprises are therefore faced with a continual change in order to keep pace with this development. This requires both innovative new products and efficient change and implementation processes. Owing to the high IT usage, both in the products and services themselves, as well as in their production and deployment, enterprise architecture management has the important task of adapting the IT used in an enterprise to changing business requirements and enabling modified business models. For example, an enterprise architecture consists of applications that support business processes and technologies that are part of the applications and enable them. Due to the high complexity of the enterprise architecture, the requirement of quick changes leads to great challenges.
The aim of the research work is to support the employees responsible for the change of an enterprise architecture by a method for decision making. The method is based on a physically constructed laboratory at Reutlingen University, the so-called Management Cockpit. This room, consisting of several screens, makes it possible to view a situation from different perspectives in parallel and to identify dependencies between them.
Modelling and Detection of Conflicts in Information Access Policies of Hospitals
Hospitals as crucial facilities of public health systems are categorized as critical infrastructure and are also constrained by additional regulation due to the sensitivity of the processed medical data. In acknowledging this strong correlation between safety and security, public administrations merged formerly separated safety and information security programs into consolidated guidelines that are considering information security as a fundamental corner stone of maintain the availability, safety, and proper functioning of such critical infrastructure.
The information security of the processed data, applications, and health IT systems is safeguarded through an information security management (ISM) and its defined objectives and controls assure a proper regulation of access to facilities that process information as well as the disclosure of protected health information. The rules for any legitimate system access or information disclosure are documented in regulatory, compliance, and enterprise constraints, however, are usually not immediately machine-processable. Access Control Systems (ACS) are utilized to formalize and combine any relevant constraints into commonly processable rulesets. Attribute-based Access Control (ABAC) is one model capable of implementing a top-down-driven ISM in a hospital environment with the inherent advantage of explicitly concentrating on formalizing, combining, and processing access and disclosure regulation through sets of policies. The latter contain legally binding rulesets, enterprise objectives, and general information security concerns in a formalized and processable technical representation.
However, the multitude of simultaneously applied policies with varying degrees of abstraction and an increasing use of IT in a hospital lead to an ever-growing risk of individual policies conflicting with each other. Those collisions may paralyze the ACS ability to decide on the legitimacy on access requests and cause a denial of service situation or a con dentiality breach, effectively crippling the health IT ability to function and perform properly. Therefore, assessing how these conflicts can be identified and mitigated in order to prevent illegitimately assigned access rights or violating any data disclosure laws are being observed in this work. Previous approaches to policy conflict detection cannot be transferred easily to a hospital information system because their characteristics do not consider policies of different types.
By means of the Design Science Research approach this work constructs both a semantic policy model and related specific conflict categories as so-called design artifacts. Both will be applied and evaluated in a conceptual application environment. One significant foundation of the work is, among other sources, the nationally applicable orientation guide for hospital information systems “Orientierungshilfe Krankenhausinformationssysteme” (OH-KIS) of the Working Group for Health, Social Affairs and Technology of the Federal and State Privacy Commissioners.
Using the design artifacts, conflicts in and between access control policies, patient privacy policies, and information security policies can be recognized, effectively enabling a focused mitigation or ideally a correction. Therefore, the management of a hospital information system is supported on a tactical and operational level.